Vulnerability Assessment Always-on insight into your security gaps
Our vulnerability assessment tool gives you a continuously updated view of your security posture so you can respond faster.
See the full picture, then fix it
See everything, everywhere
Automatically scan applications across Windows, macOS, and Linux. Get a clear picture of vulnerabilities in your environment so nothing slips through the cracks.
Focus on what matters
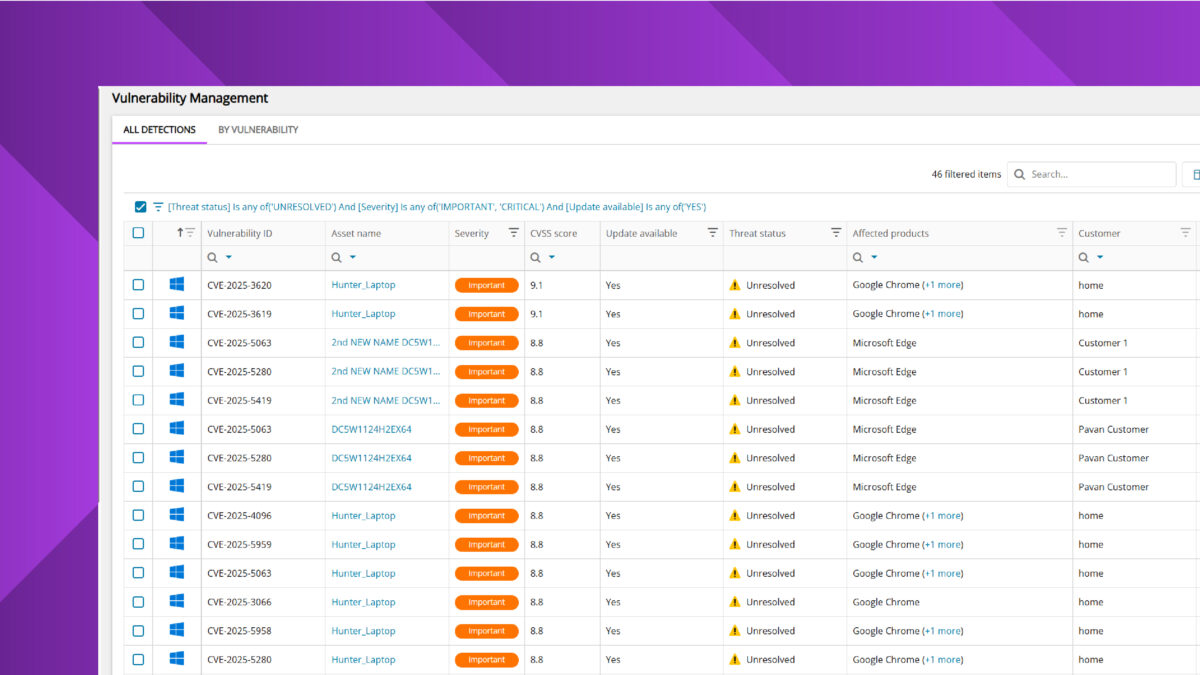
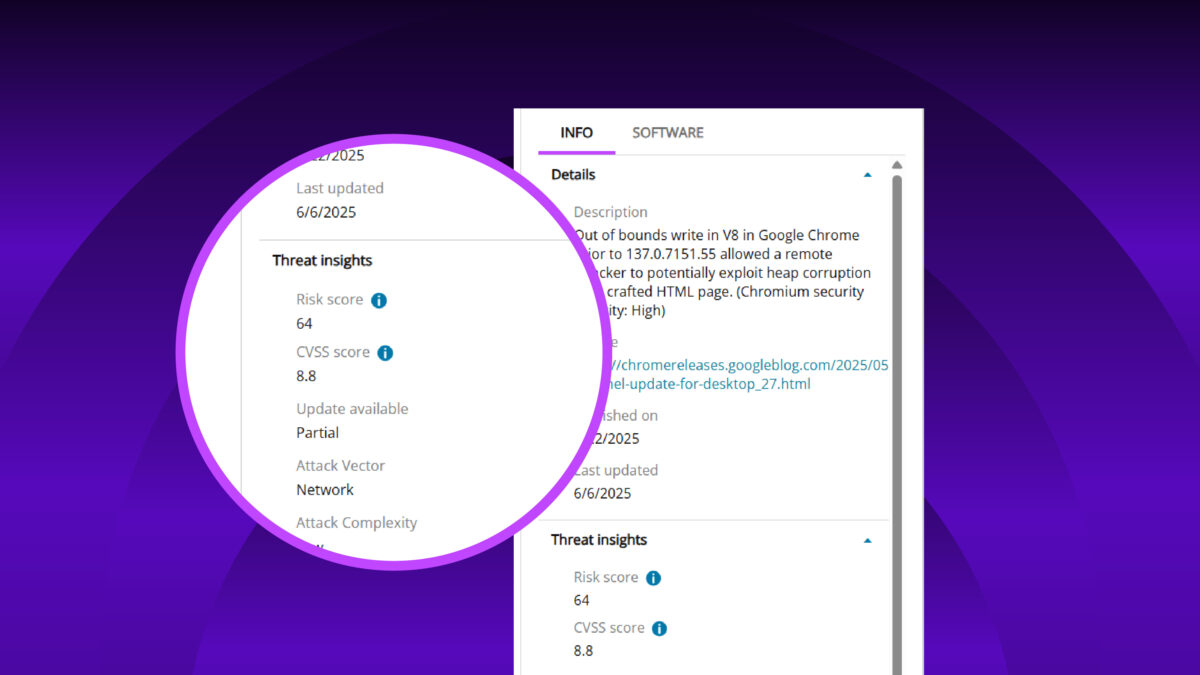
Don’t get overwhelmed by alerts. Our tool prioritizes risks using CVSS scores and exploitability indicators like CISA-KEV, helping you tackle critical threats first.
Fix issues now
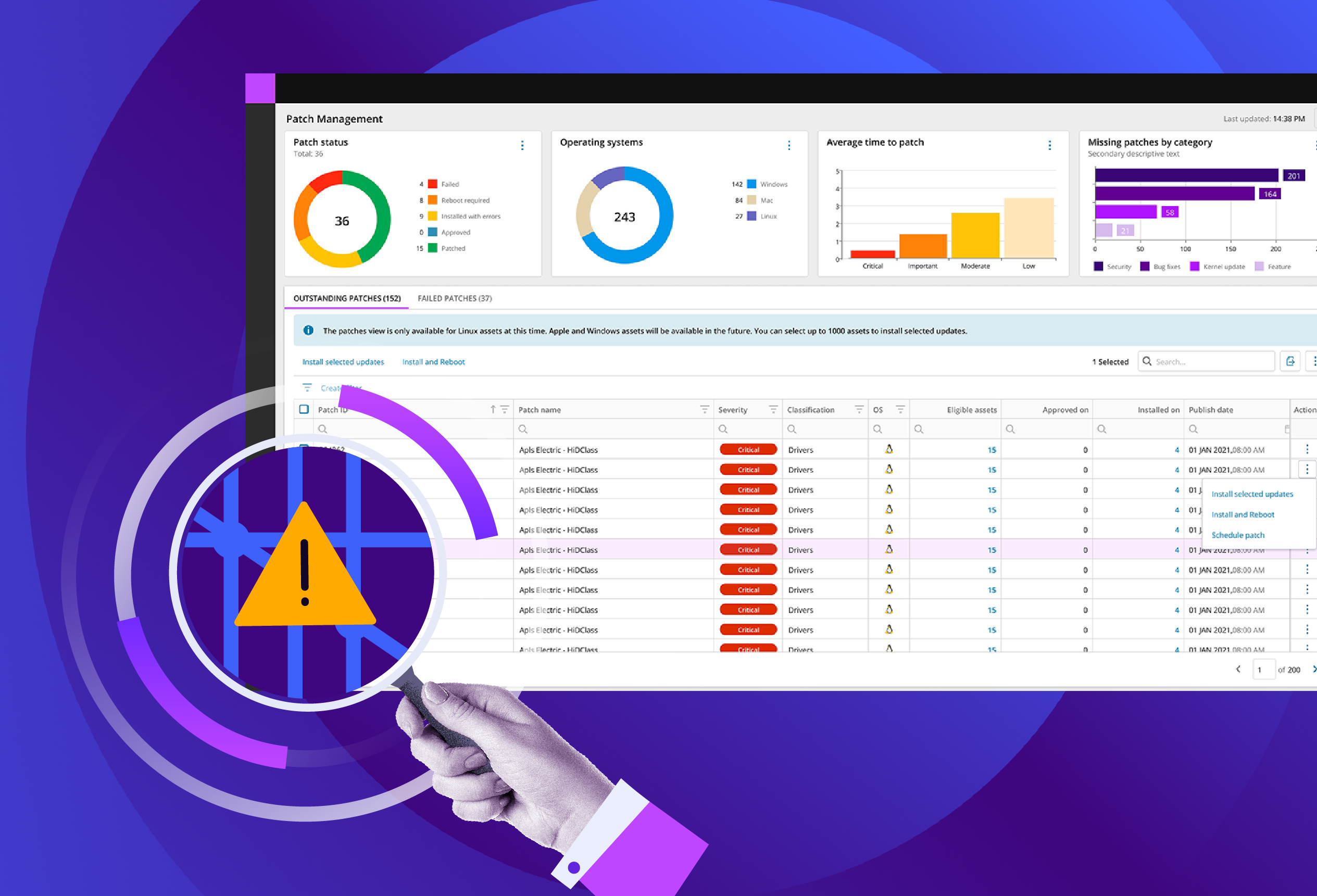
Stop switching between tools to get the job done. With integrated patch management, you can identify a vulnerability and deploy a fix immediately from the same console.
Unified workflow
Manage vulnerabilities alongside your standard IT operations. By combining assessment and remediation, you reduce friction and improve your team’s efficiency.

Find the right vulnerability assessment solution for you
N‑central
Powerful UEM with built-in vulnerability management for complex environments
- Massive scalability designed for growing IT networks
- Advanced automation with granular control
- On-premise or hosted options for maximum control
N‑sight
All-in-one UEM solution with built-in vulnerability management
- Cloud-first, get up and running in minutes
- Easy-to-use interface for immediate impact
- Best for organizations who need a quick start
FAQs
Why do I need a vulnerability assessment solution?
Why do I need a vulnerability assessment solution?
A vulnerability assessment is a key part of maintaining true business resilience. Cyberthreats evolve rapidly, and unpatched software or misconfigured devices create open doors for attackers. By conducting regular vulnerability assessment, you go beyond just scanning for weak points. An assessment involves analyzing and understanding these vulnerabilities, helping you prioritize risks, meet compliance requirements, and develop strategies to reduce your attack surface before an incident occurs.
How does this solution analyze and review vulnerabilities?
How does this solution analyze and review vulnerabilities?
Our solution provides continuous visibility by running automated frequently, as often as every six hours. It checks applications across your endpoints to detect outdated software and security gaps. Findings are cross-referenced against global threat intelligence databases including CVE, CVSS, EPSS, and the CISA KEV catalog. This enables you to move beyond simple detection to intelligent prioritization, allowing you to focus on the most critical and exploitable risks first.
Is Vulnerability Assessment a standalone software?
Is Vulnerability Assessment a standalone software?
No, and that is designed to save you time. Our vulnerability assessment capabilities are fully built into our UEM platforms, specifically N‑sight and N‑central. This means you do not need to deploy a separate agent or manage a different console. You get a unified view of your assets, allowing you to move from detection to resolution in a single workflow.
Which operating systems are supported?
Which operating systems are supported?
Our scanning capabilities cover a wide range of environments. You can detect and manage vulnerabilities across Microsoft Windows, macOS, and Linux workstations and servers, ensuring comprehensive coverage for your entire fleet.
Is remediation included in your vulnerability management tool?
Is remediation included in your vulnerability management tool?
Yes. Because our vulnerability management tool is built directly into our endpoint management platforms, you can bridge the gap between detection and action. You can leverage built-in patch management workflows, automation scripts, and software management features to remediate threats immediately, without ever leaving the platform.









