Unified Endpoint Management Unified endpoint management built for scale and security
N‑central helps you manage, secure, and monitor every device with best-in-class security and advanced automation—turning your endpoints into a resilient first line of defense.
Managing endpoints shouldn’t mean managing chaos
Unable to scale the way your business needs?
- Scale operations with flexibility that can adapt to your way of working
- Converge IT and security operations to unify your people, process, and technology
- Create your ideal connected technology stack for end-to-end business processes
Having trouble maintaining service levels and budgets?
- Standardize policies across thousands of endpoints
- Slash manual labor with AI-guided troubleshooting
- Make data-driven intelligent decisions that reduce waste and drive ROI
Carrying too much security risk?
- Real-time visibility eliminates blind spots and drift
- Automated and continuous hardening enforces endpoint security
- Shift from reactive firefighting to proactive resilience
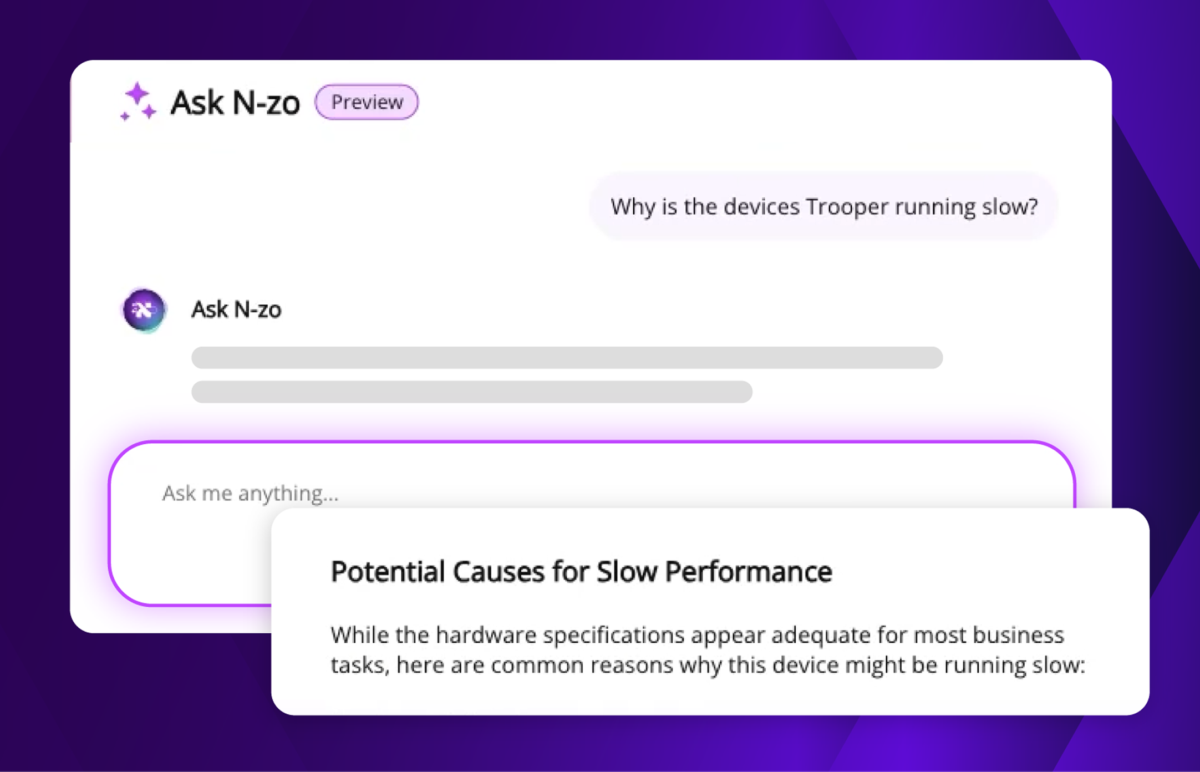
AI that understands your environment in seconds
N-zo brings AI directly into your workflow — answering questions, surfacing risks, and accelerating decisions without leaving the console.
Product Expert Agent
Product Expert Agent
Stop digging for answers. Get them before the call ends — with up to 80% efficiency gains.
- Ask product questions without leaving the console
- Get product answers with source links, instantly
- Find the exact report you need, first time
- Describe a problem in plain language
- Diagnose root cause before the call ends
- Steps, specs, and fixes — in plain English
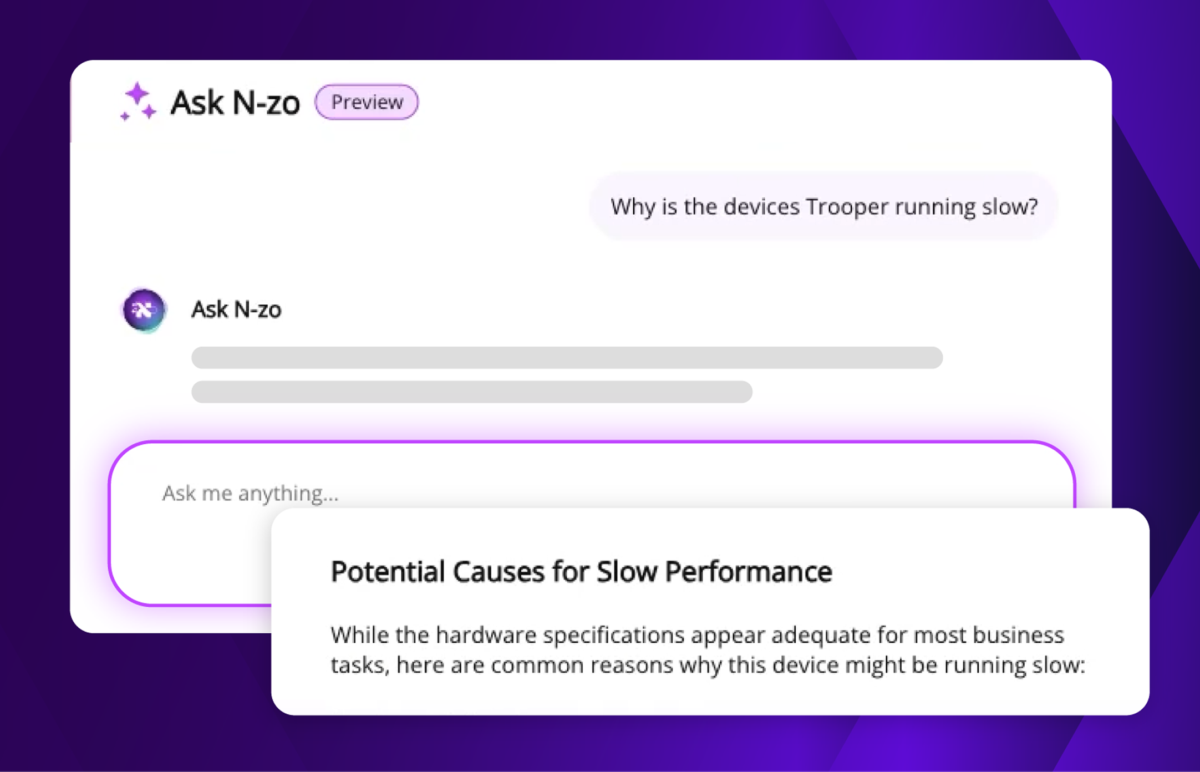
Asset Expert Agent
Asset Expert Agent
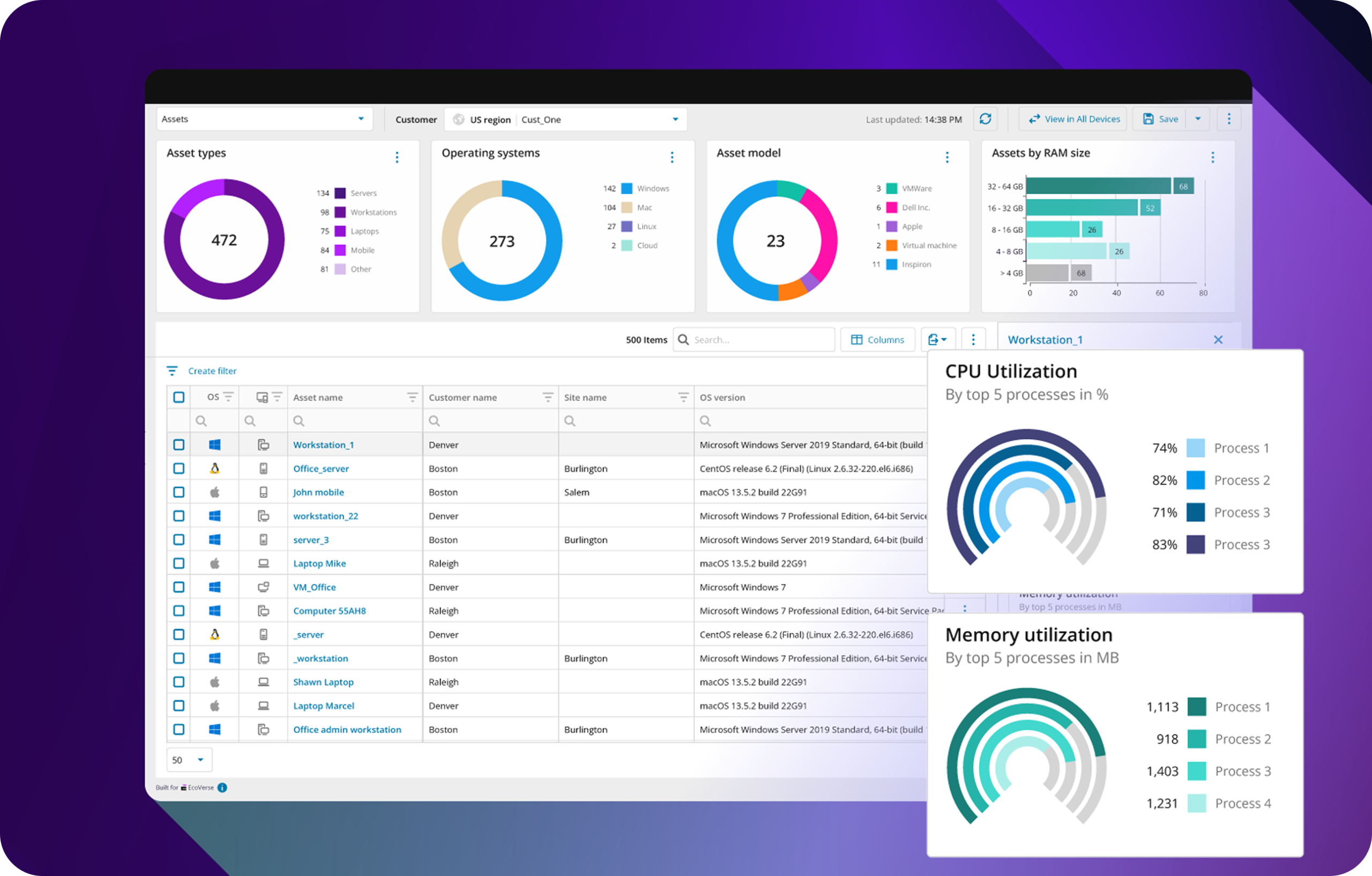
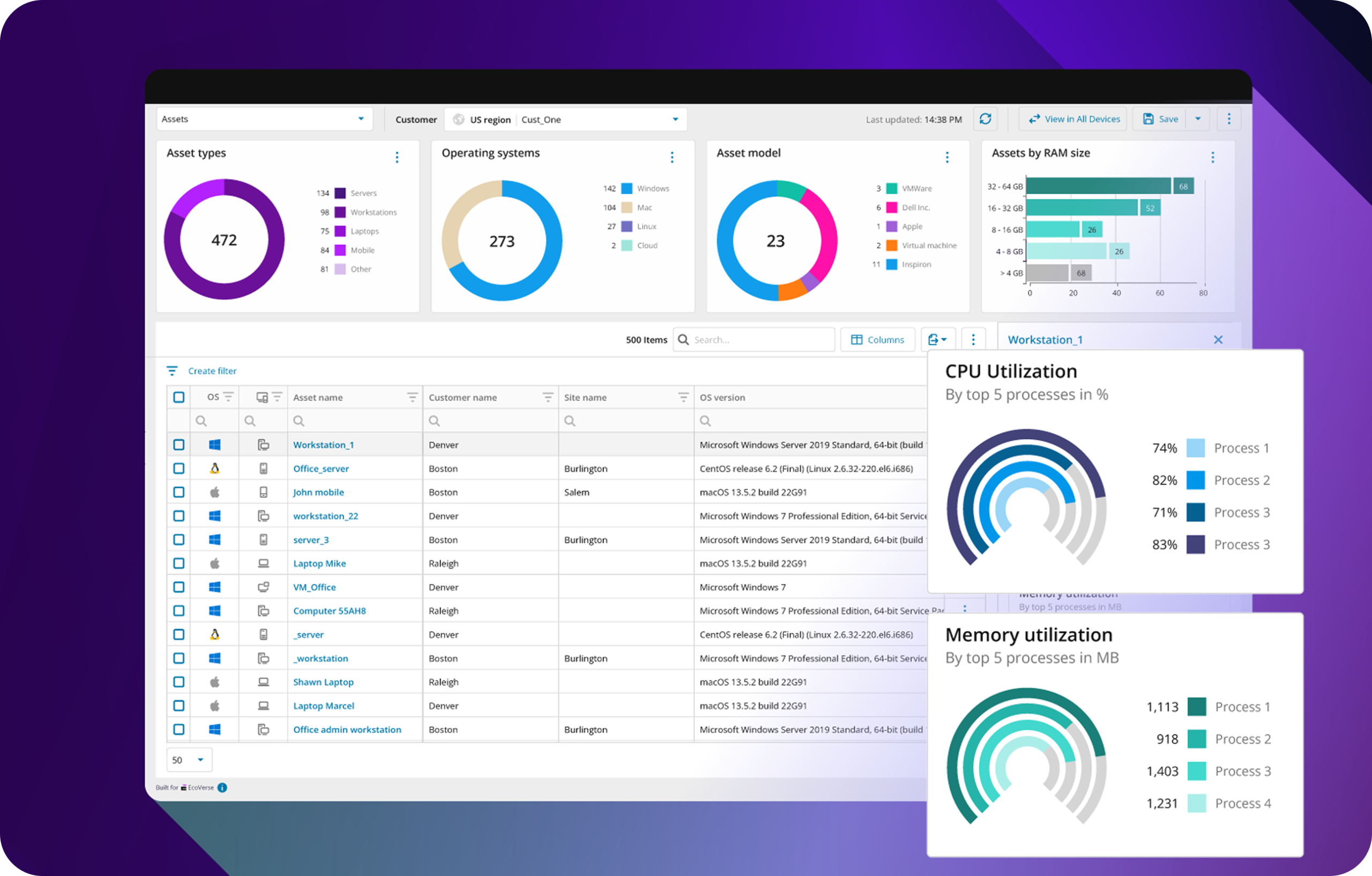
Your environment, fully visible — with up to 53% more efficient asset management.
- Why is “CEO-laptop” running very slow?
- Instantly resolve device-to-user ownership
- Surface unencrypted devices across your fleet
- Find devices offline 30+ days automatically
- Flag suspicious naming patterns and missing data
- Reduce asset risk after staff changes
Security Expert Agent
Security Expert Agent
Know your exposure before your users do.
- Surface devices below your risk threshold
- Get CVE numbers and remediation priorities
- Check CVE exposure across all devices instantly
- See what’s patched — and what still isn’t
- Walk into every QBR already informed
MCP Server
MCP Server
Connect your tools. Let your systems do the work.
Check hardware readiness before OS upgrades
- Know which devices can’t run new software
- Right-size licenses before purchasing
- Export environment health as a technician checklist
- Feed findings directly into your custom agents
- Connect systems for true agent-to-agent automation
Using N‑central gives us the visibility and automation we need to stay ahead of issues. Instead of waiting for devices to fail, we can proactively manage our estate and support rapid growth. The ability to mass-deploy kiosk updates and integrate alerts into our ITSM has been a game-changer.”
Dan DickerHead of IT, PLK Chicken UK
100 sites and growing
5 min issue resolutions
Key Pillars of Endpoint Resilience
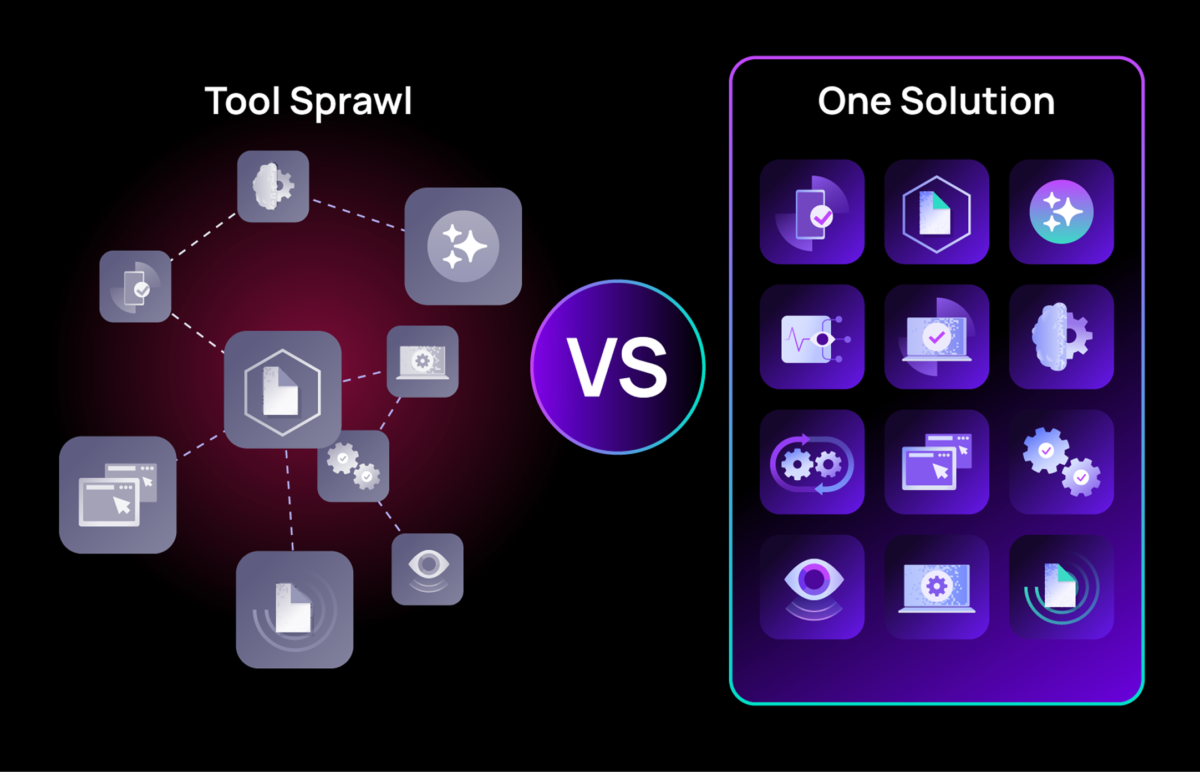

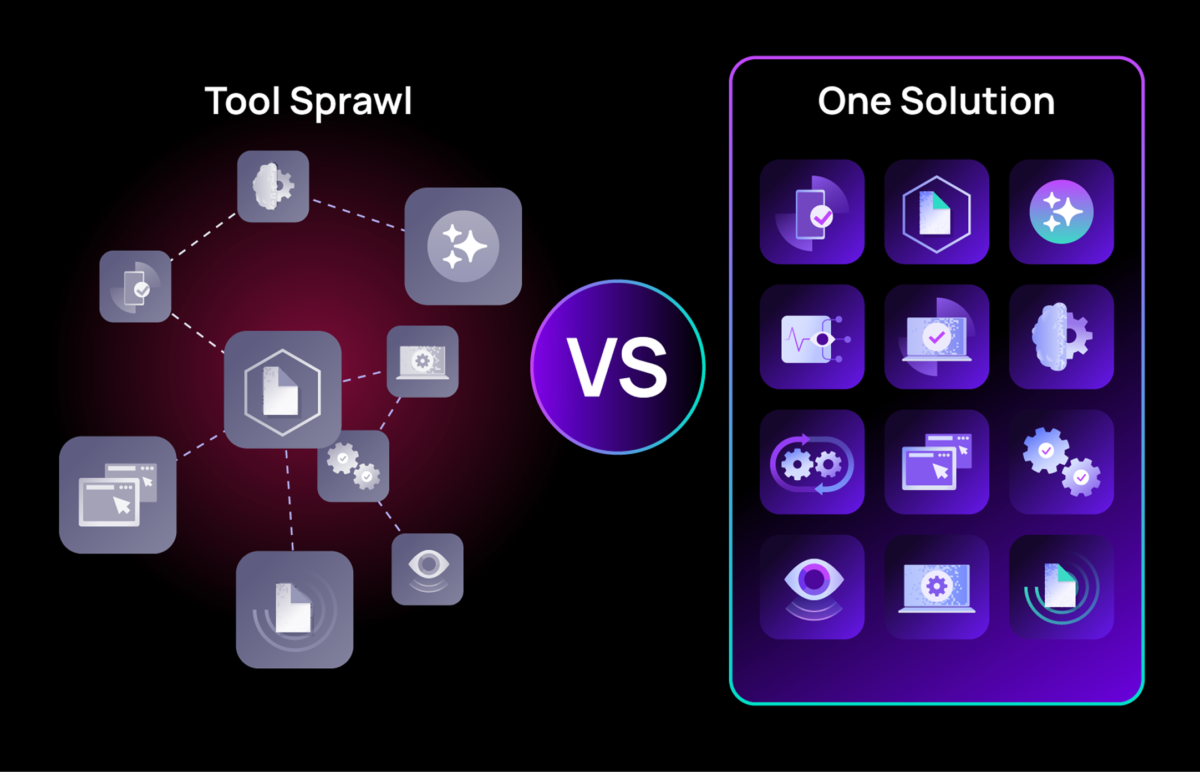
Consolidate IT point solutions
Consolidate IT point solutions
Stop tool sprawl. One console for assets, remote access, patching, and security.
Eliminate the overhead and risk of fragmented tools by unifying asset management, monitoring, remote access, and security into a single platform. The consolidation frees budget for strategic initiatives like AI adoption and data modernization.
Real-time visibility and management
Real-time visibility and management
Instant insight. Zero-touch onboarding. No blind spots.
Gain immediate oversight of your entire endpoint estate. Automatically onboard new devices with precise configurations and detect failures the moment they begin—not after users report them.

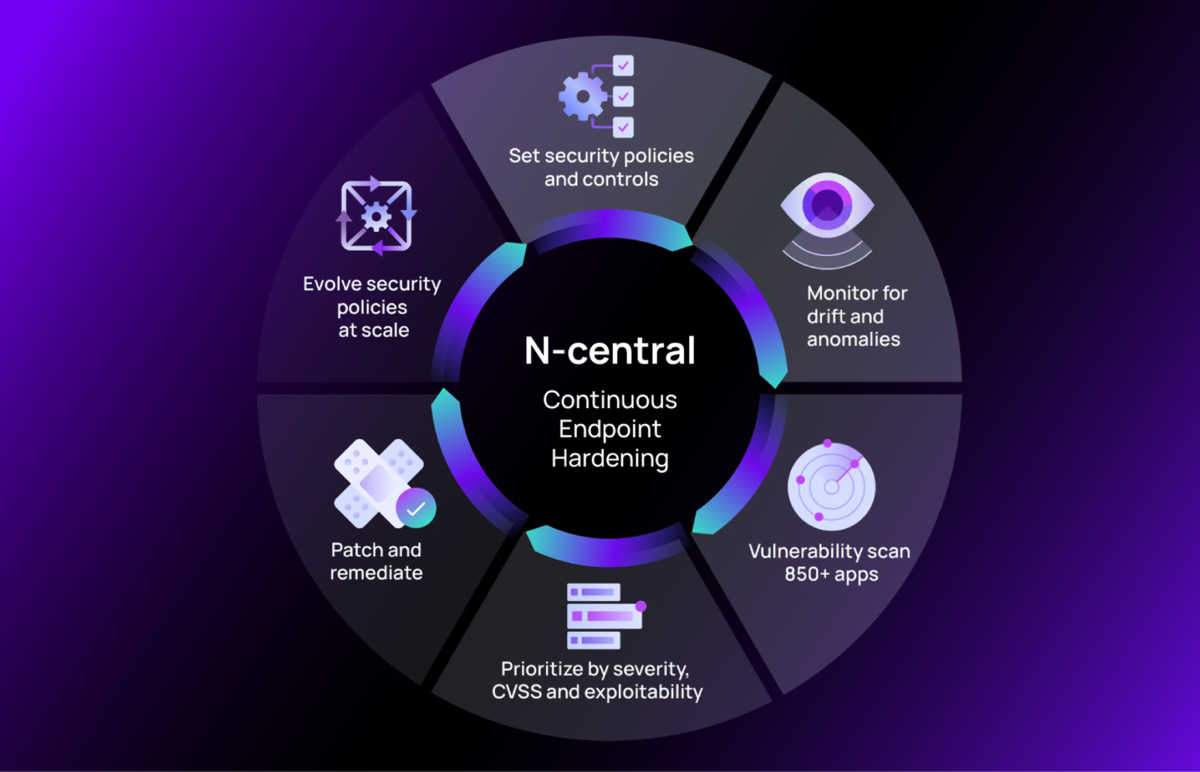
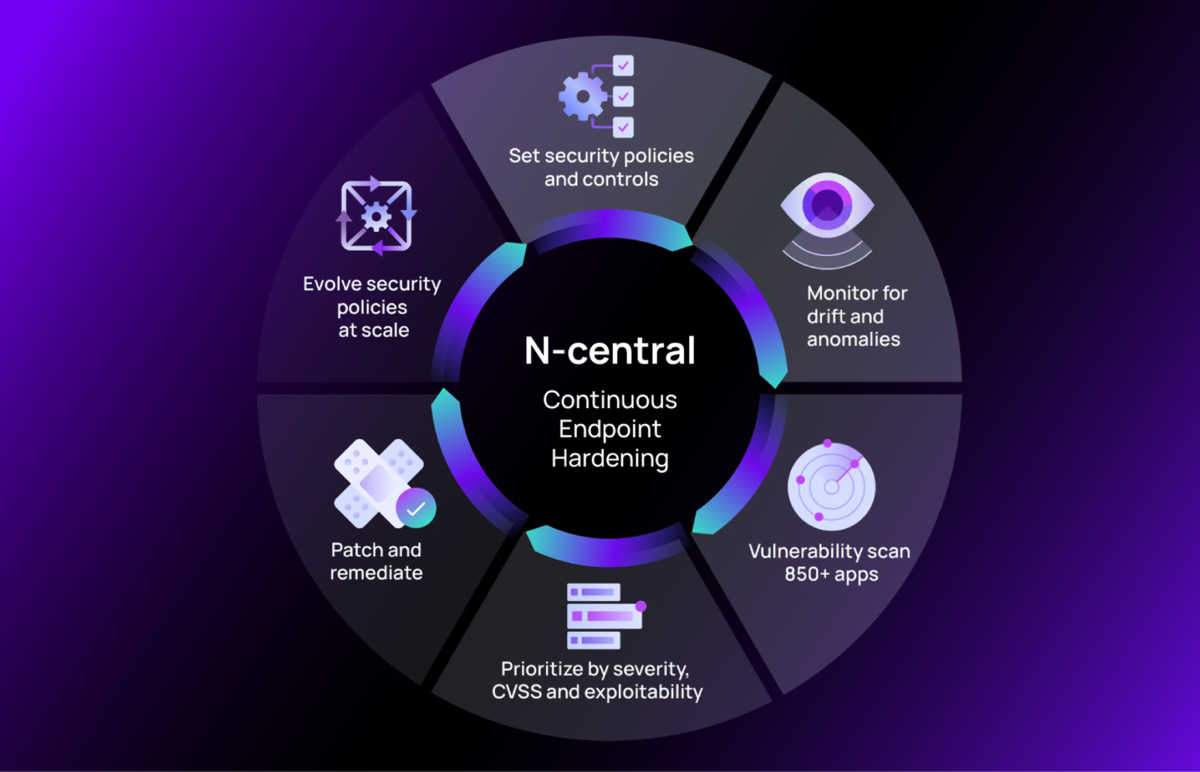
Autonomous endpoint security
Autonomous endpoint security
Self-healing resilience. Automated policy hardening.
Minimize risk with automated security policy deployment aligned with top frameworks. Create a continuous cycle of hardening, drift monitoring, and proactive vulnerability remediation at scale.
Powerful IT automation
Powerful IT automation
Broadest automation breadth. Maximized team performance.
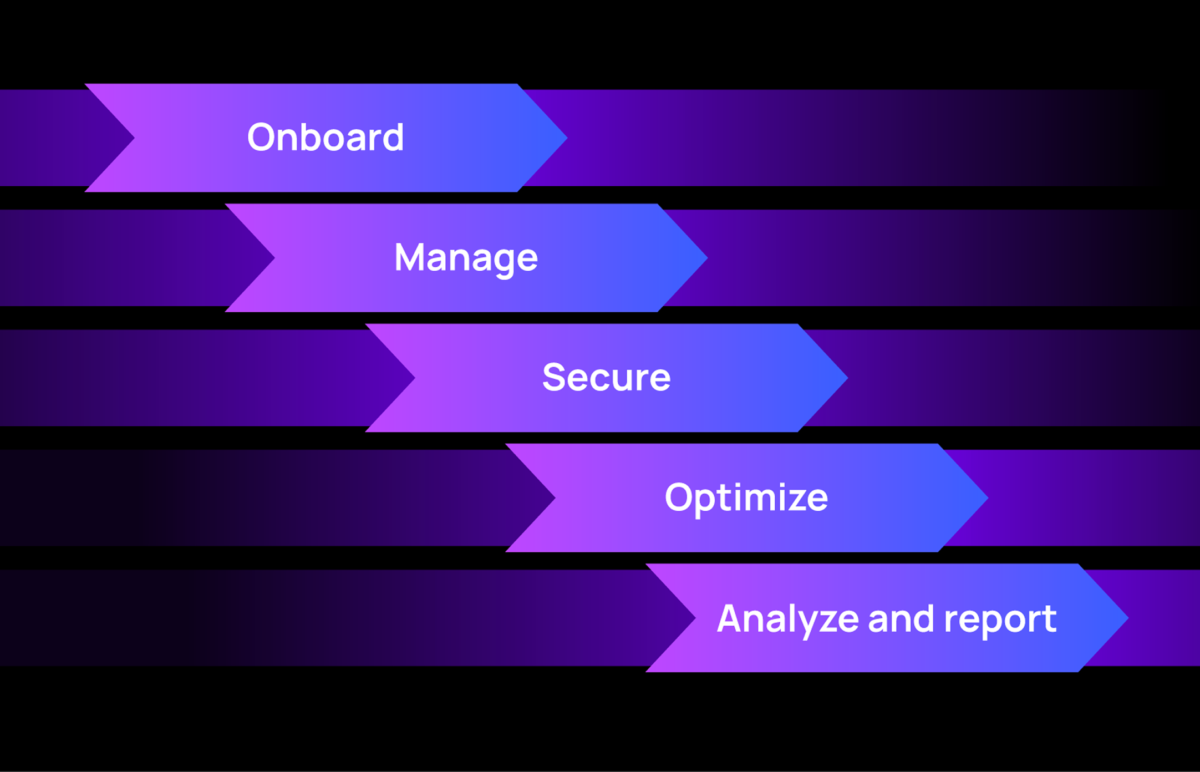
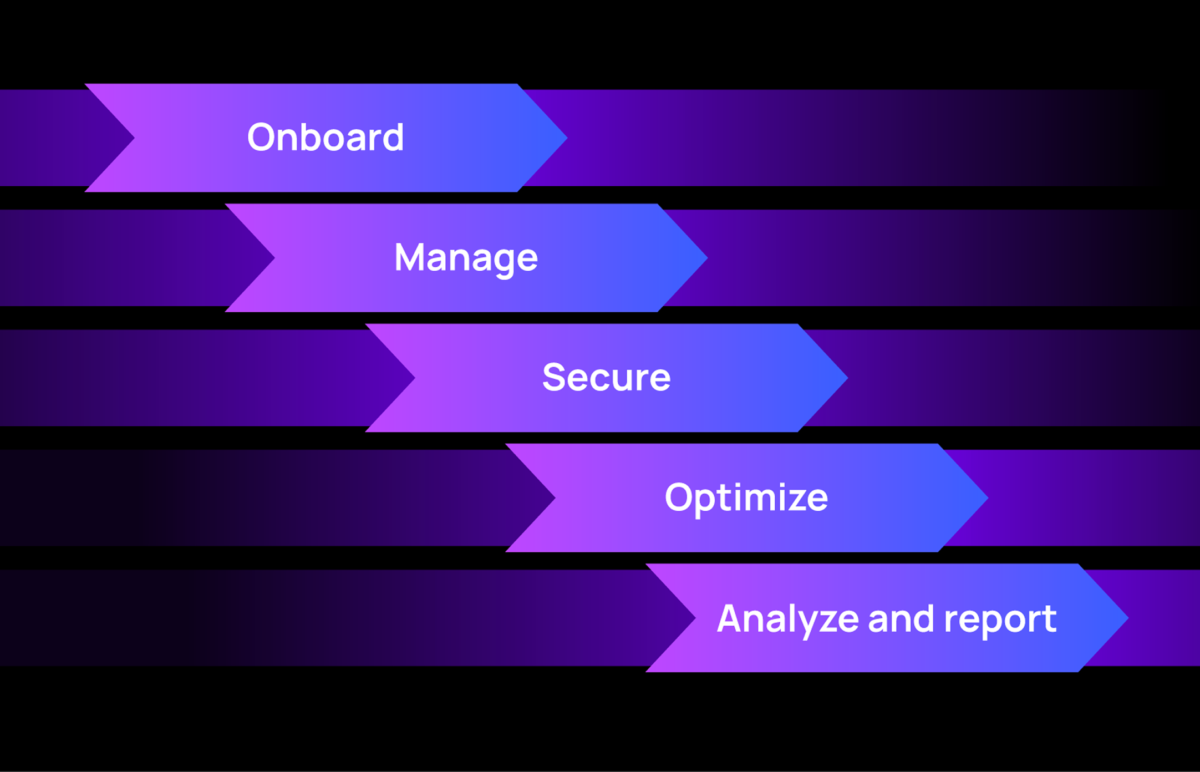
Leverage the industry’s most expansive automation toolkit. Drive standardization from onboarding to analytics, amplifying team efficiency and ensuring predictable operational outcomes everywhere.
AI-powered intelligence with
N-zo
AI-powered intelligence with N-zo
Your integrated AI assistant for real-time troubleshooting and orchestration.
N-zo provides proactive assessments, real-time troubleshooting guidance, and adaptive orchestration that scales with your infrastructure, turning raw telemetry into actionable insight.
What you can do with N‑central
Teams choose N‑central because it's built different
Resources
Frequently Asked Questions
What is Unified Endpoint Management, and how is it different from RMM?
What is Unified Endpoint Management, and how is it different from RMM?
UEM is the evolution of Remote Monitoring and Management (RMM). Where RMM typically focuses on PCs and servers, UEM extends to every endpoint type—Windows, macOS, Linux, iOS, Android, and IoT—managed from a single console. N‑central is built as a UEM platform from the ground up.
How does UEM differ from traditional MDM or EMM?
How does UEM differ from traditional MDM or EMM?
Mobile Device Management (MDM) handles mobile devices. Enterprise Mobility Management (EMM) adds mobile apps and content. UEM brings all endpoint types—desktops, servers, mobile devices, and network infrastructure—under one platform, reducing tool sprawl and centralizing security and compliance.
What device types and operating systems does N‑central support?
What device types and operating systems does N‑central support?
N‑central supports Windows, macOS, and Linux workstations and servers; network devices like routers, firewalls, and printers; iOS and Android mobile devices; and cloud infrastructure, including Microsoft 365, Azure, and Intune. The monitoring agent deploys in minutes on supported devices.
What security capabilities are included?
What security capabilities are included?
N‑central includes automated vulnerability scanning, patch deployment, real-time threat detection, encryption management, and software control enforcement. It also integrates with leading EDR, XDR, and MDR solutions. For organizations pursuing CMMC 2.0 certification, N‑central provides features aligned with NIST SP 800-171.
Can N‑central help with compliance requirements?
Can N‑central help with compliance requirements?
Yes. You can automatically enforce policies aligned with frameworks like NIST, generate compliance reports via built-in Power BI analytics, track patch status and vulnerability remediation across all endpoints, and maintain audit trails for access and configuration changes.
What automation and AI capabilities does N‑central offer?
What automation and AI capabilities does N‑central offer?
N‑central’s Infinity Core™ engine transforms real-time telemetry into adaptive workflows. You can build automations with a drag-and-drop interface, generate scripts with AI-Assisted Scripting, or use 700+ pre-built community scripts. Automation covers scheduled patching, self-healing responses, policy-driven configuration, and software installations.
How does N‑central handle mobile device management?
How does N‑central handle mobile device management?
N‑central secures company-owned and BYOD mobile devices with remote wipe, encryption enforcement, and application distribution, managed from the same console as your desktops, servers, and network devices.
Every minute without proactive resilience is one you can't afford.
Book a demo and learn from a specialist how N‑central fits your environment, or start a free trial and see the platform firsthand.