Risk-Based Vulnerability Management Stop drowning in a sea of vulnerability alerts
N‑able’s Risk-Based Vulnerability Management (RBVM) software cuts through the clutter by helping you prioritize the threats that pose the biggest risk to your business.
Make your security strategy smarter with a risk-based approach
Get complete visibility
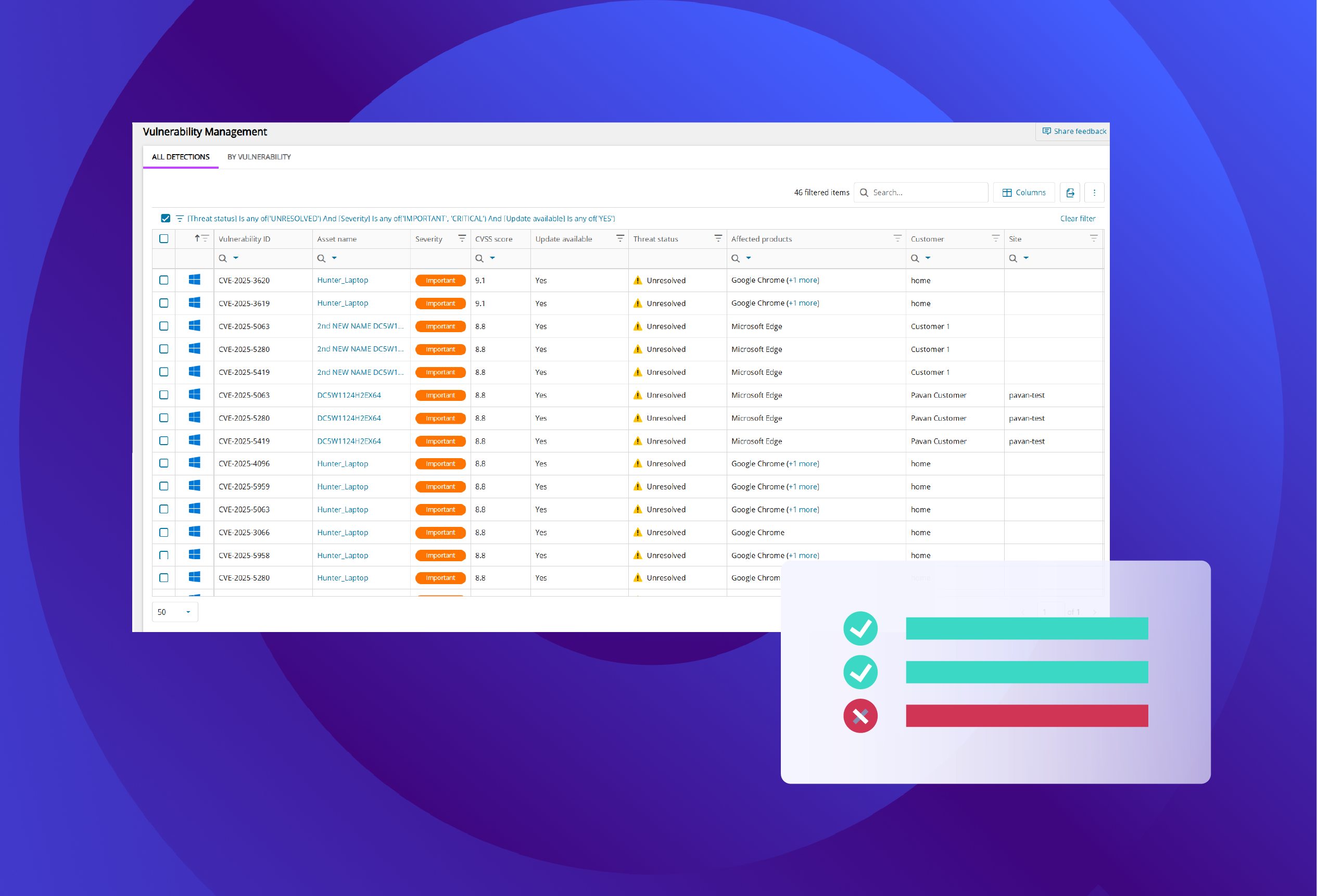
See vulnerabilities across your Windows, macOS, and Linux endpoints. With automated scans of over 900 third-party apps, you’ll get key details like severity scores and CVE data to quickly assess your environment.
Prioritize with precision
Go beyond basic scans. Our risk-based vulnerability management tool uses threat intelligence, severity scores, and real-world exploitability to prioritize the most critical vulnerabilities requiring your attention.
Manage risk, not just alerts
Our RBVM approach focuses on strategic risk management, offering insights to help you decide whether to patch, mitigate, or monitor a threat based on its business impact.
Unify your security and IT workflows
Stop switching between tools. RBVM is built directly into our N‑able UEM platforms, allowing you to identify, prioritize, and remediate vulnerabilities within a single, efficient workflow.
Unlock better vulnerability management with the right UEM solution
N‑central
Powerful endpoint management for complex networks with deep customization and control.
- Vulnerability Management included by default
- On-premises or hosted deployment
- Advanced automation and scripting
- Extensive third-party integrations
N‑sight
Cloud-based solution for MSPs and IT teams needing a fast, scalable, all-in-one tool.
- Includes Vulnerability Management at no extra cost
- 100% SaaS with an intuitive UI
- Rapid deployment and onboarding
- Built-in PSA and ticketing features
Frequently asked questions
How does N‑able RBVM tool work?
How does N‑able RBVM tool work?
Our risk-based vulnerability management software is integrated directly into our N‑central and N‑sight platforms. It continuously scans for vulnerabilities across your managed endpoints, analyzes them against threat intelligence and business context, and presents a prioritized list so you can remediate efficiently.
How is risk-based vulnerability management different from traditional vulnerability scanning?
How is risk-based vulnerability management different from traditional vulnerability scanning?
Traditional scanners often produce long lists of vulnerabilities with little context, leading to alert fatigue. Our RBVM approach helps you understand which issues are most likely to be exploited and would have the biggest impact, enabling a more strategic and effective response.
How does your software calculate a vulnerability's risk score?
How does your software calculate a vulnerability's risk score?
Our composite Risk Score is calculated using multiple data points for a more accurate picture of risk. It incorporates the standard CVSS score but enriches it with data on exploit prevalence, whether it’s part of the CISA KEV database, its association with known ransomware, and its age. This helps you stack rank threats more effectively than relying on CVSS alone.
What operating systems are supported?
What operating systems are supported?
Our risk-based vulnerability management tools provide complete visibility for vulnerabilities across all major operating systems, including Windows, macOS, and Linux, all from a single dashboard.
Resources
Evolve your security posture from reactive to resilient
Ready to see how a risk-based approach can transform your security posture? Take control with a tool that helps you work smarter.







