How we patch: The art of patch management

We all know how important it is to stay current with security updates or “patches.” But how many organizations are really following best practices? As attackers get more sophisticated and researchers become more diligent, vulnerabilities in popular software—from operating system to end user applications and even security software – are discovered every day. To their credit, software vendors are working overtime to stay on top of the problem and issue patches to fix these flaws as quickly as possible.
This never-ending flow of updates from multiple vendors, though, can make it difficult for IT to keep up. While Microsoft and other major software-makers try to simplify the patching process through automation and distribution tools, we all know that in the corporate environment, it’s often prudent to test patches in a lab environment before rolling them out to your production network.
Failure to do so can result in a nightmare of system problems and even computers that become unbootable. Who can forget McAfee’s patch fiasco in 2010, when an update rendered Windows XP computers unusable and the company ended up having to reimburse many customers for the repairs required to restore functionality?
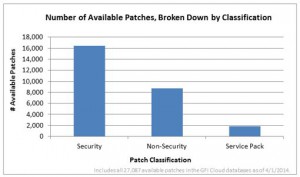
However, failure to patch can have even more serious ramifications—including the exposure of confidential company or personal information and consequent civil liability and/or penalties for violation of regulatory compliance requirements—since the majority of patches issued are security-related. A look at a year of statistics collected from the LOGICnow database reveals that out of the 27,087 patches, more than 16,000 are security patches, and almost 2,000 more are service packs, which typically contain many security updates.
In today’s uncertain economic climate, many IT departments are understaffed and admins’ workloads are already heavy. Patching can become a “when I get around to it” thing—and that can be a recipe for disaster. Some patches may slip through the cracks completely, and trying to keep track manually of which systems are patched and which aren’t is, at best, an administrative headache.
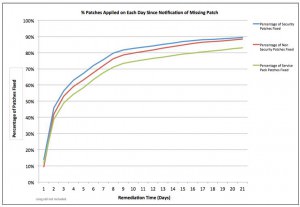
A good patch management system goes a long way to address these problems. Such a system can monitor for missing patches and notify admins. Recent statistics collected regarding organizations using LOGICnow’s products shows that notification is a powerful motivator, with more than 30% of missing patches applied within one day of notification, and almost 90% fixed within two weeks.
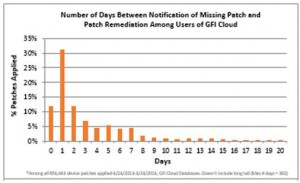
These statistics span the period of one year, from April 2013 to April 2014, and are based on 864,106 device patches applied by customers over that time frame. Keep in mind that these numbers and patterns apply specifically to LOGICnow’s customers, who may differ from the average small business users. In fact, a study last year from the Federation of Small Businesses in the UK indicated that only 36 percent regularly installed security patches on their computers. Meanwhile, vulnerable systems are putting many organizations at serious risk.
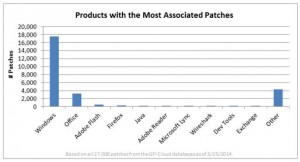
Part of the problem is that there are so many patches for so many different software products. The data showed that those with the greatest number of patches over the year included Windows, Microsoft Office, Adobe Flash, Firefox, Java, Adobe Reader, Microsoft’s Lync Communications software, Wireshark, Exchange, and various developer tools. There were also more than 4,000 patches associated with “other” products.
Keep in mind that pure numbers don’t always tell the full story, though. At first glance, one might assume that the “patchiest” products shown above have the most vulnerabilities. That might or might not be the case. For example, in a recent month, Microsoft issued five patches addressing seven vulnerabilities. During that same month, Apple released only two patches, but addressed 20-something vulnerabilities. In other words, total number of patches doesn’t necessarily equate to the most vulnerabilities.
It’s also difficult sometimes to compare products across vendors because of different means of releasing patches. For instance, some vendors always issue a new version of the software to patch security issues rather than releasing standalone individual patches. (Google Chrome is one example.)
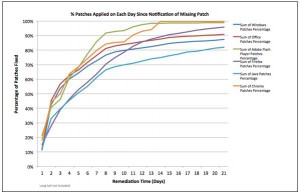
In any event, it’s worthwhile to look at a breakdown of the so-called “patchiest” products in terms of the percentage of patches applied within a given number of days following the missing patch notification. The percentage peaks earlier for some, such as Firefox and Adobe. But for all products, the patching percentage seems to follow a similar curve: a sharper increase up to about the 7th day and then it levels off.
The percentage at the one-week mark, though, depends on the product. For Firefox, it’s greater than 90% while slightly less than 70% for Java.
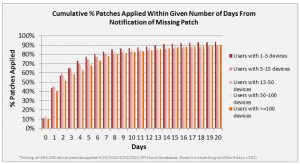
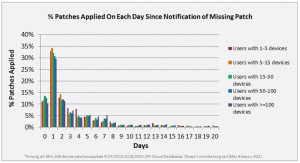
Another pattern that remains fairly consistent over the course of the first week is that companies with more than 100 devices tend to have patched a smaller percentage of those devices on any given day. This isn’t surprising, since larger companies are more likely to proceed with caution, testing patches before applying. It also just takes longer to get a larger number of devices patched. Up until around the 4th day following notification, the smallest companies (between 1 and 5 devices) lag slightly behind in patching as well. But after the 4th day, they consistently have the largest percentage of devices patched.
The good news is that regardless of company size, the largest percentage of LOGICnow’s customers are applying patches within one day after receiving notification that they’re missing.
This reinforces the hypothesis that notification is a strong motivating factor.
As might be expected, the numbers indicate that companies are applying security patches a bit more quickly and diligently than non-security patches. However, the difference isn’t great. On the other hand, there is a bigger gap between the application of regular patches and full-fledged service packs. This isn’t surprising, either, since it generally takes more time to roll out service packs, and test them beforehand due to the complexity and increased risk of “unintended consequences.”
All in all, these statistics tell an encouraging story: Whereas some industry-wide surveys show much lower percentages of devices patched, particularly in certain segments such as small business, users of automated hosted management platforms are “getting it done.” They are responding quickly to notifications of missing patches and remedying the problems within days. It makes sense that over-burdened IT personnel can use a helping hand, and given the dire consequences that can result when systems go unpatched, putting a high priority on patch management is a smart business decision.
By Debra Littlejohn-Shinder